Stateful vs. Stateless: Breaking Down Authentication Architectures
Learn the difference between stateful and stateless authentication, how session-based and token-based methods work, and how to choose the right approach for your application architecture.
We've all been there: starting a new project, and the first task is building the login system. It’s surprisingly easy to get wrong. At its core, modern authentication hinges on one key question: How does the server remember you between clicks? Since HTTP is stateless, each request starts fresh, meaning the server has no memory of prior actions. To keep users logged in, we need a method to exchange an "ID card" with each request.
Developers typically use two main strategies for this: Stateful (Session-based) and Stateless (Token-based) authentication. Let’s explore how both methods work, their challenges, and how to choose the right one for your app.
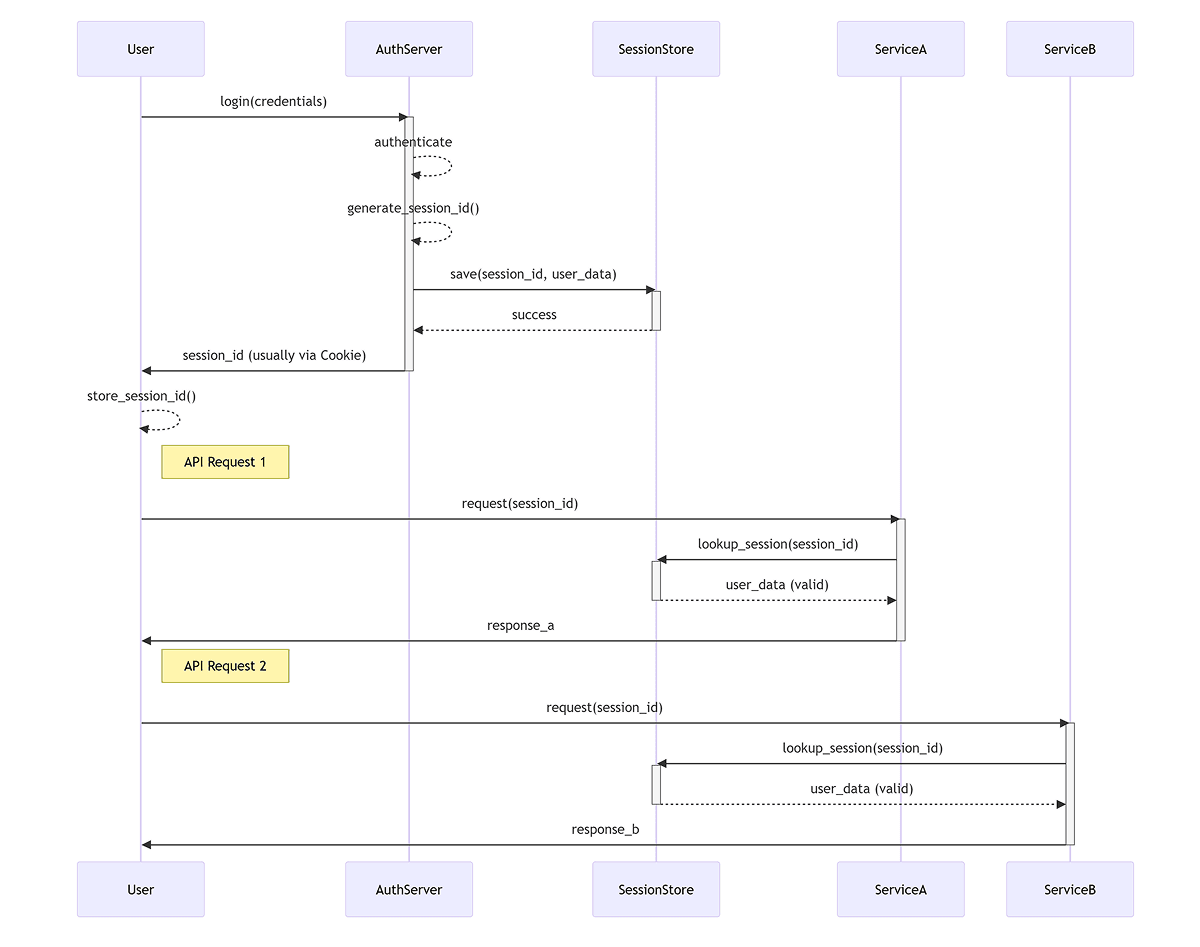
The Old Reliable: Stateful (Session-Based) Authentication
Stateful authentication is the traditional method that web applications have been using to manage logins since the 90s. You can think of it like a library system with a check-out process. It’s termed "stateful" because the server actively maintains a record (the state) of every logged-in user in its memory or a database.
How it works
- •The Login: You provide your credentials (username and password) to the server.
- •The Check-Out: The server verifies your password. If everything checks out, it generates a random, unique "Session ID" and records it in its database (or a fast cache like Redis).
- •The Library Card: The server responds to your browser, providing that Session ID within a Set-Cookie header. (Tip: always mark this cookie as HttpOnly and Secure).
- •Subsequent Requests: Your browser is clever. Every time you click on a link or request data, it automatically sends that cookie back to the server.
- •Validation: The server examines your cookie, checks its database to see if that Session ID is active, and grants you access.
The Pros
- •Instant Access Control: Since the server checks the database with every request, logging someone out is straightforward. If an admin revokes a user's access, they simply delete the Session ID from the database. The user's access is terminated almost immediately.
- •Simplicity: It’s a well established method. Almost all classic web frameworks already include robust session management.
- •Security by Design: Remember that the HttpOnly flag prevents client-side JavaScript from accessing the cookie, significantly reducing the risk of Cross-Site Scripting (XSS) attacks that could compromise your session.
The Cons
- •Scaling Challenges: This is the major downside. If your application suddenly gains many users and you add a second server, Server A might log the user in, but if Server B handles their next request, it has no idea who they are. To resolve this, you need to set up a centralised, shared session database (e.g., a Redis cluster), which introduces infrastructure complexities and latency.
- •Mobile Apps and CORS: Cookies are designed for web browsers and specific domains. If you have a separate API (api.example.com) and a frontend (app.example.com), managing Cross-Origin Resource Sharing (CORS) can be complicated. Plus, native mobile applications (iOS/Android) don’t work with cookies natively, requiring you to implement a workaround.
- •CSRF Vulnerabilities: Since browsers automatically attach cookies, there's a risk of Cross-Site Request Forgery (CSRF) where a malicious actor can trick your browser into sending an unwarranted request. To mitigate this risk, you need to implement anti-CSRF tokens.
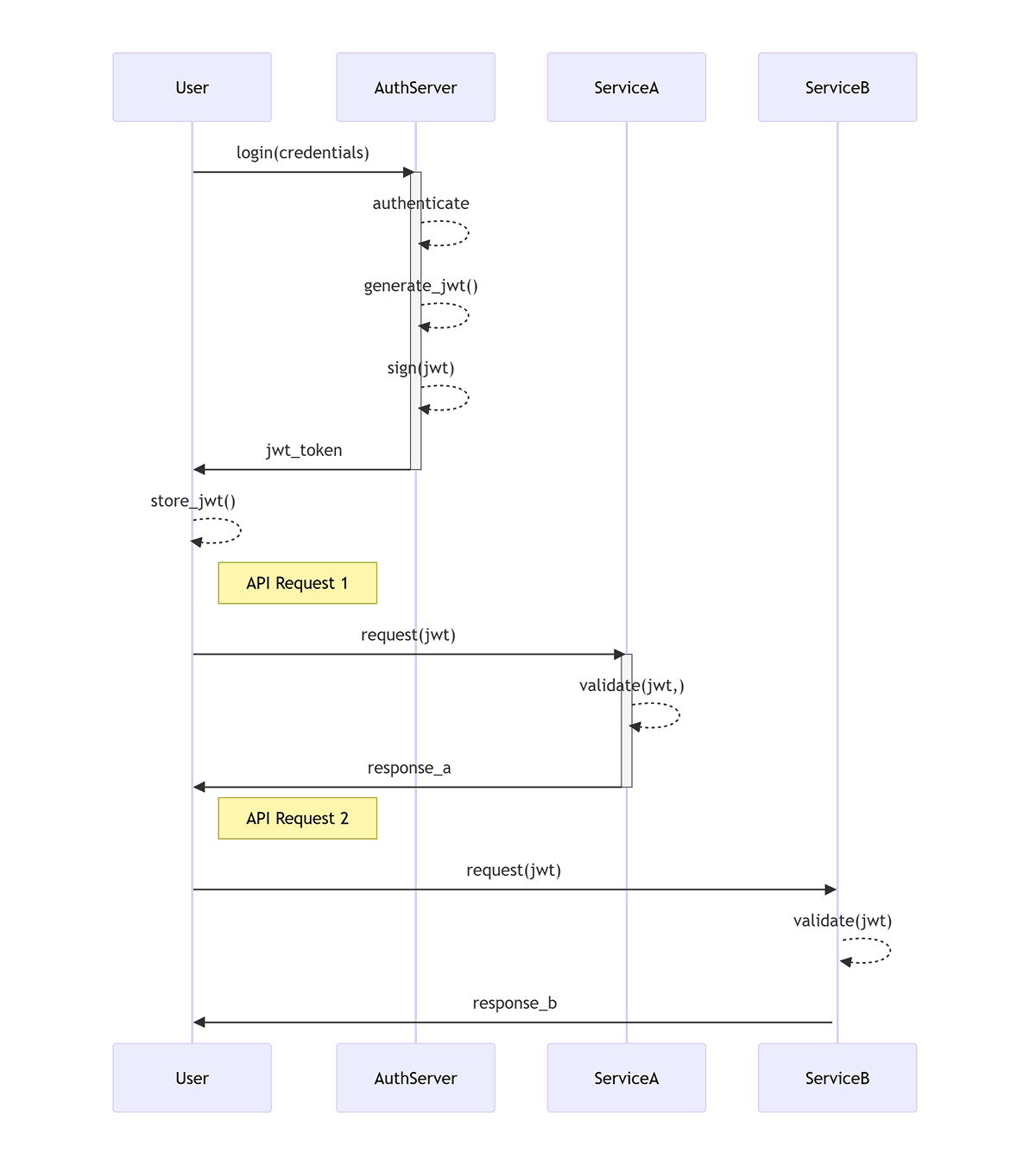
The Modern Challenger: Stateless (Token-Based) Authentication
As Single Page Applications (SPAs) and microservices took over the world, developers got tired of pinging a central database on every single request. We needed a way to instantly verify users across different domains and servers.
Enter stateless authentication, usually powered by JSON Web Tokens (JWTs). Instead of keeping records, the server acts like an ID agency: it issues you a cryptographically forged proof ID and then completely forgets you exist
How it Works
- •The Login: You send your credentials to the server.
- •The ID: The server verifies your identity and issues a JWT. This token contains a payload (such as your user ID and an expiration date). The server then mathematically signs it using a top-secret key.
- •The Handoff: The server sends this JWT back to your app.
- •Subsequent Requests: Your frontend app stores the token and manually attaches it to the Authorisation header of every subsequent request (e.g., Bearer eyJhbGciOi...).
- •Validation: The server receives the request, checks the token, and runs the math against its secret key to verify the signature. If it hasn't been tampered with and hasn't expired, the server trusts it. No database lookup required.
The Pros
- •Infinite Scalability: Since the server doesn't need to look up a session in a database, you can spin up 10,000 API servers globally. As long as they all share the same secret key, they can verify JWTs independently and instantly.
- •Microservice and Cross-Domain Friendly: JWTs don't care about domains or CORS. You can get a token from auth.example.com and use it to grab data from api.anotherservice.com seamlessly.
- •Mobile Native: Native mobile apps handle token-based auth much more naturally than dealing with clunky web cookies.
The Cons
- •Scaling Challenges: This is the major downside. If your application suddenly gains many users and you add a second server, Server A might log the user in, but if Server B handles their next request, it has no idea who they are. To resolve this, you need to set up a centralised, shared session database (e.g., a Redis cluster), which introduces infrastructure complexities and latency.
- •Mobile Apps and CORS: Cookies are designed for web browsers and specific domains. If you have a separate API (api.example.com) and a frontend (app.example.com), managing Cross-Origin Resource Sharing (CORS) can be complicated. Plus, native mobile applications (iOS/Android) don’t work with cookies natively, requiring you to implement a workaround.
- •CSRF Vulnerabilities: Since browsers automatically attach cookies, there's a risk of Cross-Site Request Forgery (CSRF) where a malicious actor can trick your browser into sending an unwarranted request. To mitigate this risk, you need to implement anti-CSRF tokens.
The Industry Standard: The Hybrid Approach
So, which one do you choose? In modern web architecture, we usually cheat and use both. We call it the Short-lived Access Token with a Stateful Refresh Token.
Here's the playbook: When a user logs in, the server generates a stateless JWT (the Access Token) that lives for a very short time, say, 15 minutes. It also generates a stateful Refresh Token that lives much longer (like 7 days) and saves it in the database.
Your app uses the quick JWT for all its API calls. It's fast, it scales, and if a hacker steals it, they only have a 15-minute window of chaos.
When the JWT expires, your app silently sends the Refresh Token to the server to get a brand new JWT. Because the Refresh Token is stateful, an admin can delete it from the database at any time. The next time the user tries to refresh their expired JWT, the server slams the door in their face, effectively logging them out.
The Bottom Line
At the end of the day, neither architecture is inherently "better"; they just solve different problems.
If you are building a traditional, monolithic application, save yourself the headache: Stateful Session Auth is almost always the easiest and most secure route. If you are building a highly decoupled system with a React/Vue frontend, a mobile app, and a dozen backend microservices, Stateless Token Auth (JWT) is the way to go, provided you put in the work to handle token expiration and refresh cycles securely. Understand your architecture; pick the right one.
Share this article:
Hasala Abhilasha
Associate Software Engineer
-






